
Protected Data Even if a Device Is Lost
For companies with the highest security requirements, Threema OnPrem offers a sophisticated new feature: thanks to DualLock, chats are now protected even if a mobile device is lost or stolen.

For companies with the highest security requirements, Threema OnPrem offers a sophisticated new feature: thanks to DualLock, chats are now protected even if a mobile device is lost or stolen.

New design, redesigned workflows, and additional features: Threema 7.1 for iOS offers more than just Liquid Glass.

Have you ever heard someone say they were “ghosted” and had no idea what it means? Or are you unsure what “dry texting” and being “left on read” is? In this blog post, we explain some common Internet slang terms and concepts relating to instant messaging.

Business communication belongs in secure channels, not in the photo gallery of personal smartphones. With the latest update of Threema Work and Threema OnPrem for iOS, screenshots of chat histories can now be prevented.

Today’s digital environments are more connected and distributed than ever. Traditional security models built around a trusted network perimeter are no longer sufficient. As cloud services, remote work, and mobile devices blur the boundaries of corporate networks, a new guiding principle has emerged: Zero Trust.

Several recent news reports have sparked discussion in the IT community and raised questions among some of our users. One topic is the view that paid online services are incompatible with anonymity – and therefore with strong data protection. Another is the risk of user accounts being hijacked through identity spoofing, which current events have brought back into focus.
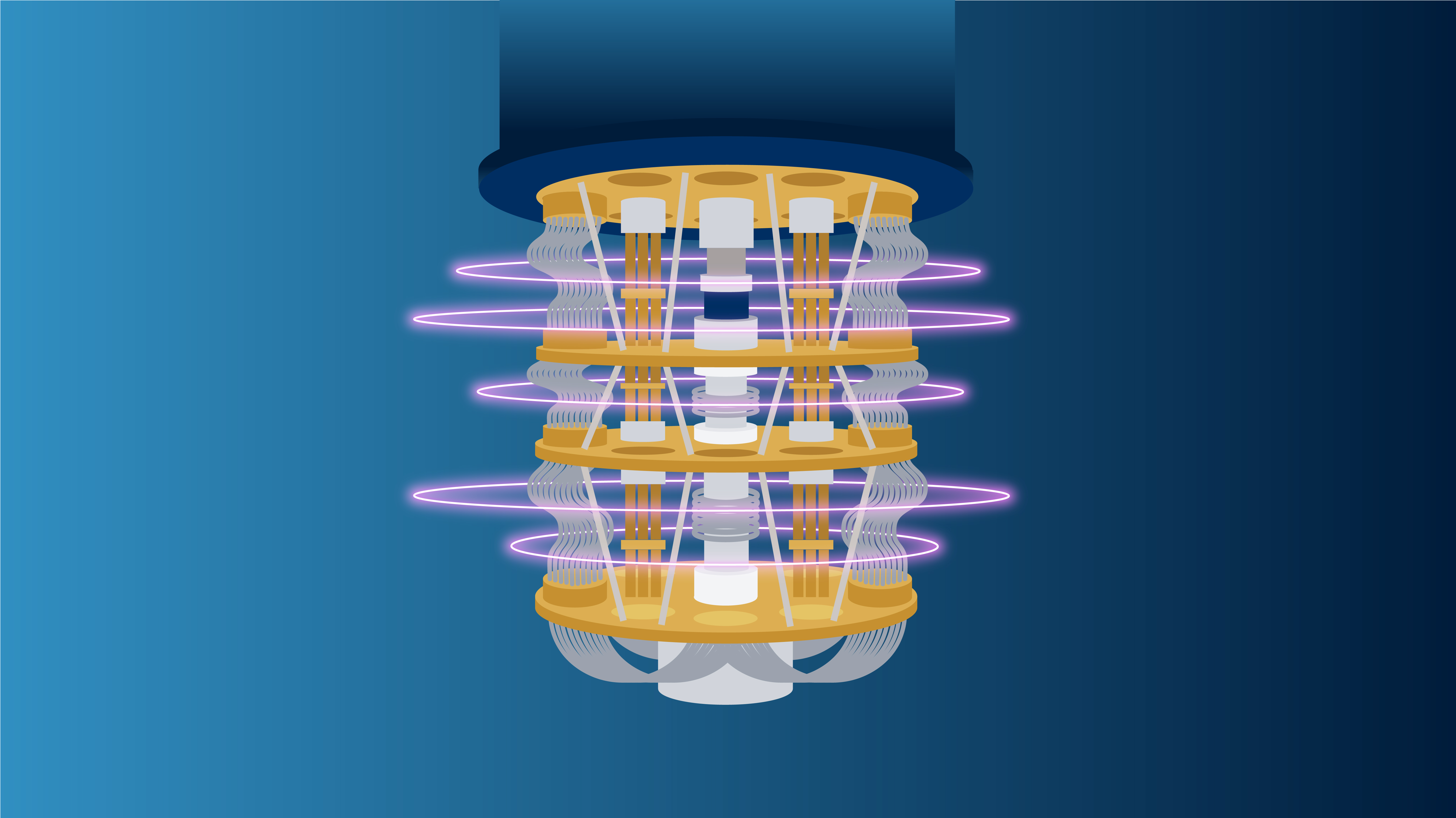
We are joining forces with IBM’s renowned research division to implement post-quantum cryptography in Threema. This collaboration will further strengthen Threema’s exceptional security standards, ensuring that our communication solutions are prepared for future threat scenarios.

Do you use the Threema Private app and know professionals who might be interested in a secure business messenger? Recommend Threema Work and earn a bonus!

As part of the critical infrastructure, the energy sector has special requirements for secure information and data exchange. With “REVIVE,” Axpo Systems provides a crisis management platform specifically developed for this sector. Threema OnPrem serves as the central communication module.